Table of Contents
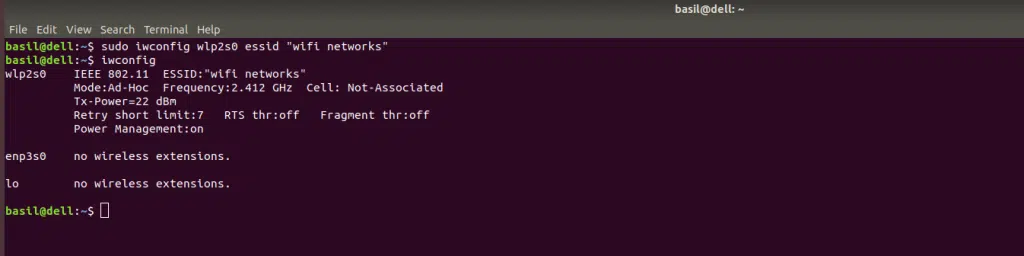
How Iwconfig Connects to WiFi:
TheIwconfig connects to the WiFi command and allows you to configure the interface of a wireless network. It also allows you to view the ESSID of the connected device, the name of the MAC protocol, the mode of operation, and the access point address. This command is useful in debugging.
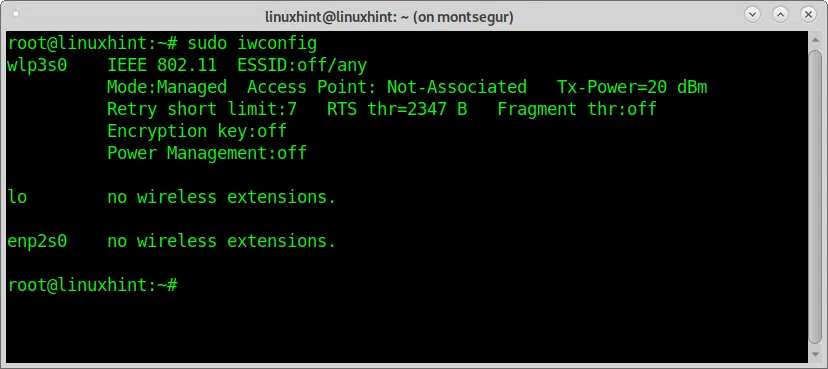
Iwconfig configures a wireless network interface:
Iwconfig is a command similar to ifconfig(8) but devoted to wireless interfaces. It allows users to configure the parameters of their wireless interfaces and may also display statistics.
The parameters can vary from device to device and are provided by the device driver. They also depend on the hardware.
Iwconfig will display the wireless network interface name and other details. It can also be used to scan available networks.
However, this feature does not work well if a network has been hidden. The iwconfig command can reveal hidden networks that are not visible when iwlist is run.
Depending on the wireless card, you can configure a fixed IPv4 or DHCPv6 address for your computer.
The first step in configuring a wireless card is to determine the device name. Linux associates device names with different wireless cards, and iwconfig can help you find the correct device name.
iwgetid reports the Iwconfig connects to WiFi:
There are a few reasons why you should use tweeted to report the ESSID of a wireless network connection.
First, it’s easier to incorporate into scripts. Second, it provides more information than iwconfig. It prints the ESSID, AP address, and mode of the current connection.
First, the ESSID is a string that describes the network that a computer connects to. For example, if your WiFi connection is on a hotspot, ingested will report the ESSID that the computer connects to.
An ESSID can contain sensitive information, such as real names or other personal information. Therefore, you should keep this in mind when using WiFi on your computer.
wpa_supplicant negotiates the authentication process Iwconfig connects to WiFi:
To connect to a WPA-secured wireless network, wpa_supplicant needs to be running. It can be started from system startup scripts or from PCMCIA-cs scripts on PC cards.
Normally, the cardmgr utility starts wpa_supplicant when the card is inserted into a PC. It then waits for the wireless interface to set up before negotiating keys with the access point.
Once you’ve run wpa_supplicant, you’ll have to configure it so that it submits the right credentials to the WPA authenticator.
Then, you’ll need to assign an IP address for authenticated users. This is a relatively straightforward process, but there are several steps to take.
Beacons are sent at regular intervals to maintain cell coordination:
Beacons are a part of wireless networks, which enable communication between multiple APs. These small packets are sent at regular intervals.
Beacons can be used to manage client stations in the coverage area of multiple APs. They also help expedite the association between APs.
This issue can be frustrating to deal with, but it can be resolved by changing the physical location of wireless devices or by adjusting the RTS/CTS function.
This issue is particularly prevalent in wireless ad hoc networks, where multiple nodes are trying to communicate at once. As a result, the hidden node is ignored by other nodes, which can result in a loss of connectivity.
The beacon interval is typically the same for all SSIDs in a band. It is typically a one-time unit every 102.4 ms, but it can be longer if required.
The longer the beacon interval, the lower the overhead on the channel. In addition, each SSID must have its own beacon.
Auto mode forces the card to reassociate with the currently best access point:
If you want your card to automatically reassociate with the best access point in the range, you must configure the Auto mode.
This mode forces the card to reassociate with the currently best access point when it senses a change in the access point signal strength. By default, the Auto mode is off.




Add comment